6. Splunk Challenge
Introduction
Angel Candysalt in the Great Room
Hey Santa, there’s some crazy stuff going on that we can see through our Splunk infrastructure.
You better login and see what’s up.
Objective
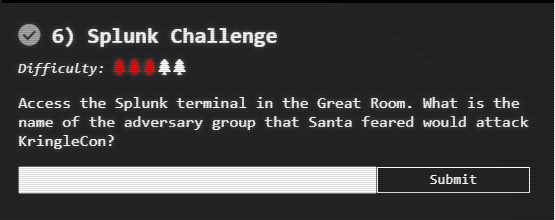
Note: The challenge is black because it is from Santa's Black Badge.
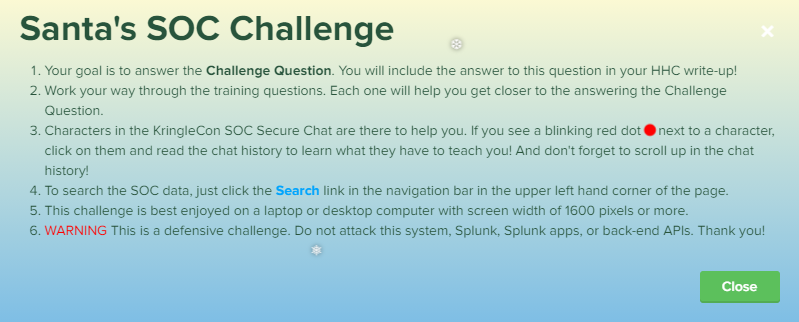
Hints
Solution
Training Questions
Question 1
Q: How many distinct MITRE ATT&CK techniques did Alice emulate?
search used: index=T* | fields index | dedup index
And then count up the results
A: 13
Question 2
Q: What are the names of the two indexes that contain the results of emulating Enterprise ATT&CK technique 1059.003?
(Put them in alphabetical order and separate them with a space)
search used: | tstats count WHERE index=T1059.003* by index | table index
A: t1059.003-main t1059.003-win
Question 3
Q: One technique that Santa had us simulate deals with 'system information discovery'. What is the full name of the registry key that is queried to determine the MachineGuid?
Go to https://github.com/redcanaryco/atomic-red-team and peruse the Windows tests in csv format
Search on the page for "system information discovery", which points to test T1082
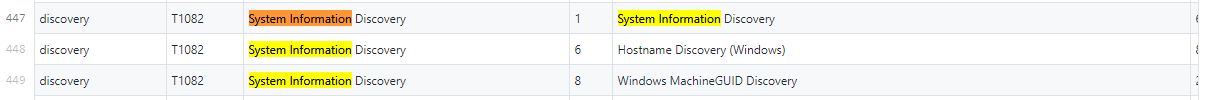
Now go to the code for the test - https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1082/T1082.yaml
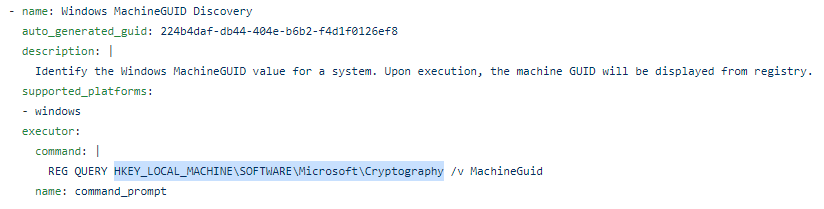
A: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography
Question 4
Q: According to events recorded by the Splunk Attack Range, when was the first OSTAP related atomic test executed? (Please provide the alphanumeric UTC timestamp.)
Search used: index=attack OSTAP
A: 2020-11-30T17:44:15Z
Question 5
Q: One Atomic Red Team test executed by the Attack Range makes use of an open source package authored by frgnca on GitHub. According to Sysmon (Event Code 1) events in Splunk, what was the ProcessId associated with the first use of this component?
The open source package is AudioDeviceCmdlets at https://github.com/frgnca
Use github search for AudioDeviceCmdlets in the RedCanary repository:
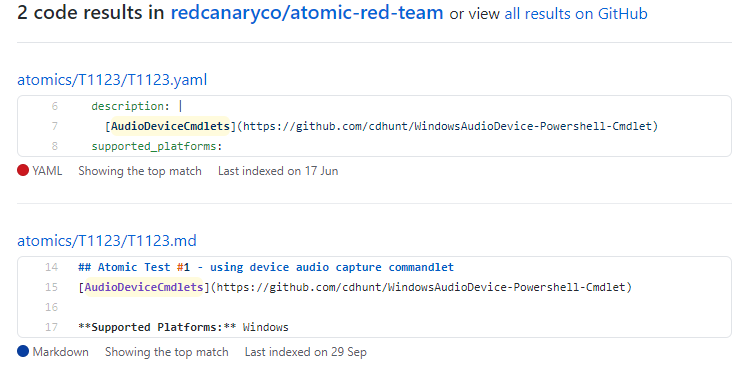
Going back to Splunk and using the search index=T1123* WindowsAudioDevice-Powershell-Cmdlet, the result is:
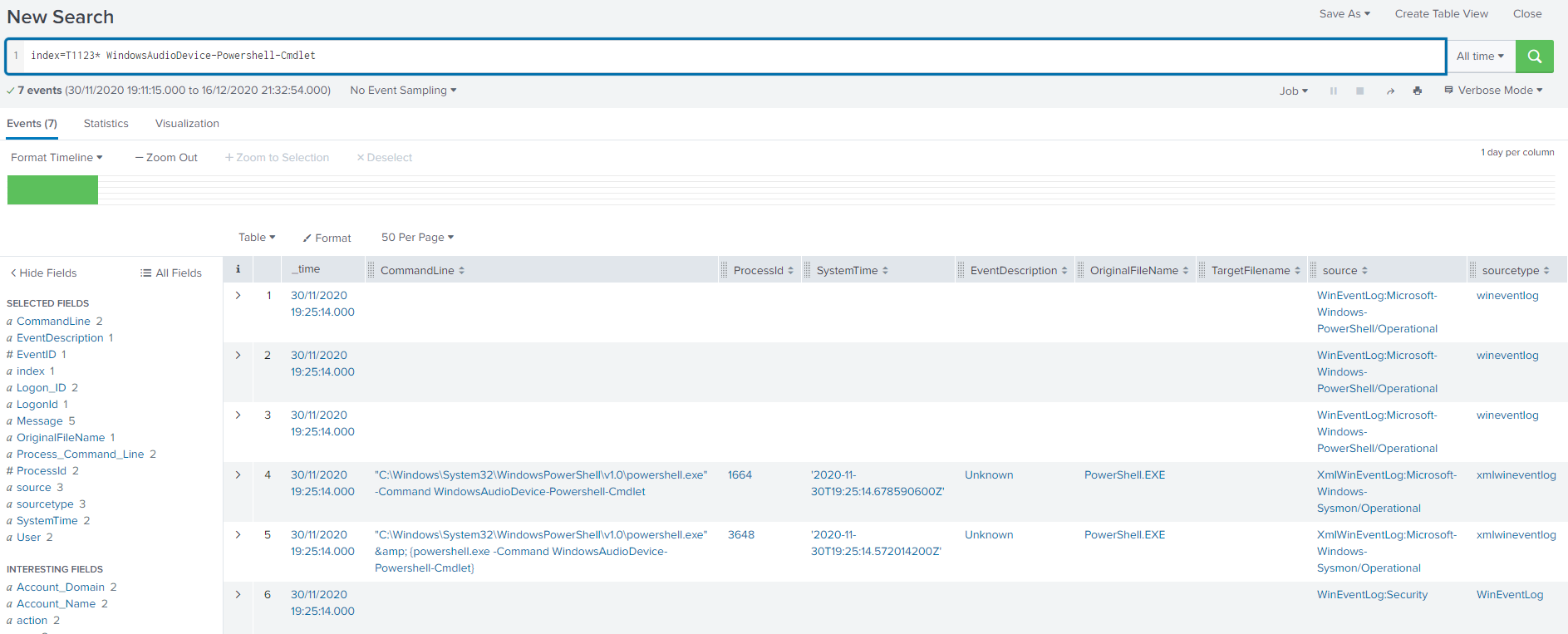
A: The ProcessId was 3648
Question 6
Q: Alice ran a simulation of an attacker abusing Windows registry run keys. This technique leveraged a multi-line batch file that was also used by a few other techniques. What is the final command of this multi-line batch file used as part of this simulation?
The technique is T1547.001 https://attack.mitre.org/techniques/T1547/001/
Search used: index=T1547.001* RunOnce

This batch file was https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Misc/Discovery.bat
A: The last line of the file is quser
Question 7
Q: According to x509 certificate events captured by Zeek (formerly Bro), what is the serial number of the TLS certificate assigned to the Windows domain controller in the attack range?
Search used: index= sourcetype=bro | fields certificate.serial, certificate.subject | dedup certificate.serial
There are 12 results and the top result was for a host called win-dc-748.attackrange.local, which from the host name would suggest that it is the Windows domain controller.
A: 55FCEEBB21270D9249E86F4B9DC7AA60
Training question Summary:
Challenge Question
The challenge question was:
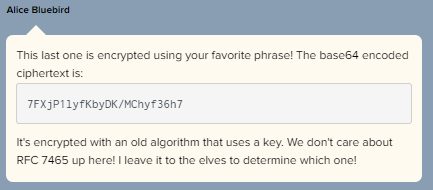
RFC 7465 is titled "Prohibiting RC4 Cipher Suites", so this is encrypted with RC4 and RC4 takes a Passphrase
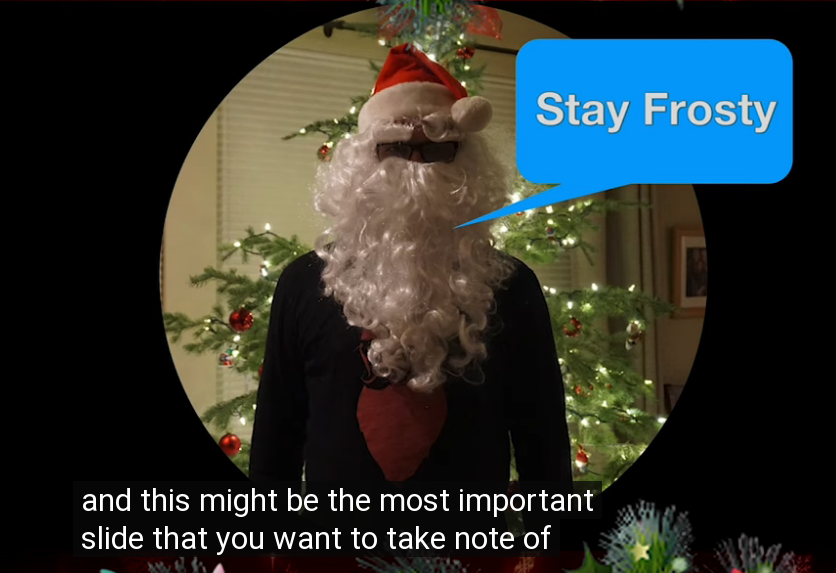
If you had watched the talk by Dave Herrald Adversary Emulation and Automation then you would have seen this at the end of the talk.
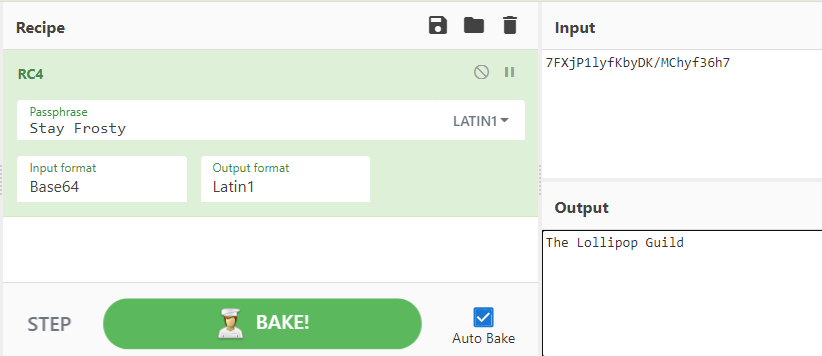
Let's use Cyber Chef to decrypt the message:
Success:
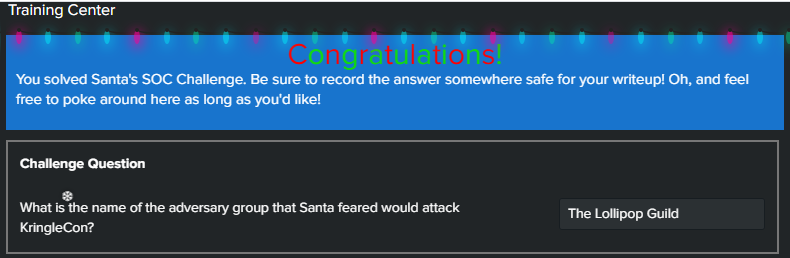
Answer
The Lollipop Guild